
Barracuda spots 7 million device code phishing attacks
Barracuda detected 7 million device code phishing attacks in four weeks and linked the rise to the EvilTokens phishing kit.
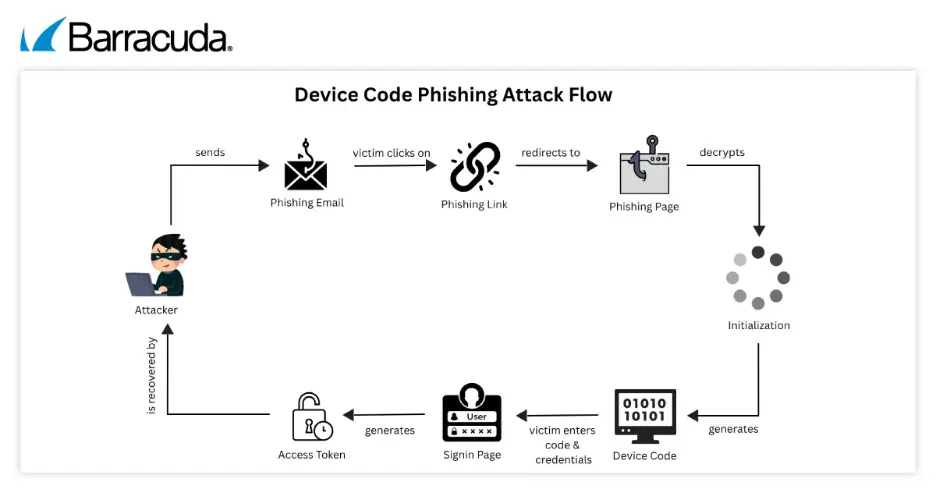
The security firm examined how attackers abuse device code authentication to gain approved access to Microsoft 365 and Entra ID environments. The method lets criminals get in without directly stealing passwords or relying on fake sign-in pages.
Device code authentication is commonly used when someone needs to sign in on one device by entering a short code on another trusted device. It is often used on devices with limited interfaces, including televisions, printers and command-line tools.
Attackers exploit that familiarity by requesting a legitimate device code from Microsoft, then sending a phishing message urging the target to enter the code on an official sign-in page. If the victim completes the process, Microsoft issues OAuth access and refresh tokens, which are then passed to the attacker.
Unlike more familiar forms of credential phishing, this approach uses legitimate authentication links rather than fake websites. That can make malicious activity harder for both email filters and users to detect.
The technique can also bypass multifactor authentication and conditional access checks because the victim authorises the device themselves. The resulting refresh token can let attackers maintain access to an account for days or weeks, even if the user later changes their password.
Why it matters
The findings point to a shift in phishing tactics, from harvesting credentials to hijacking trusted authentication flows. For organisations that rely heavily on cloud email and identity systems, the method creates a path to persistent access that may not trigger the same alerts as a fake login page or password theft.
The growth in attacks also reflects the spread of phishing-as-a-service tools, which package techniques for wider criminal use. Barracuda identified the recently reported EvilTokens kit as a driver of the surge.
Because the attack uses a genuine Microsoft login page, social engineering becomes central. Users are asked to perform an action that appears normal, especially since short verification codes are already a familiar part of linking devices and approving logins.
The analysis also highlights the challenge for defenders. Security teams have spent years training staff to spot suspicious domains and cloned sign-in portals, but device code phishing shifts attention from the link destination to the context of the request.
Security response
Barracuda urged organisations to use layered controls to reduce exposure. It pointed to advanced email filtering, identity protection measures and continuous monitoring as practical steps, alongside tighter controls around device authorisation flows.
Staff awareness also remains important, particularly around when verification codes should be entered. In device code phishing, the user is not handing over a password but is still granting access to an attacker's session.
"Device code phishing has become industrialised as part of a PhaaS model - making it a dangerous and scalable threat," said Saravanan Mohankumar, manager in Barracuda's Threat Analysis Team. "Security defences need to adapt quickly. Layered security controls, including advanced email filtering, identity protection mechanisms and continuous monitoring, can significantly limit exposure. Additionally, enforcing strict controls around device authorisation flows and raising awareness about entering verification codes only in trusted contexts can help prevent such attacks from succeeding."
