Celebrity stalkerware leak exposes private messages online
Thu, 30th Apr 2026 (Yesterday)
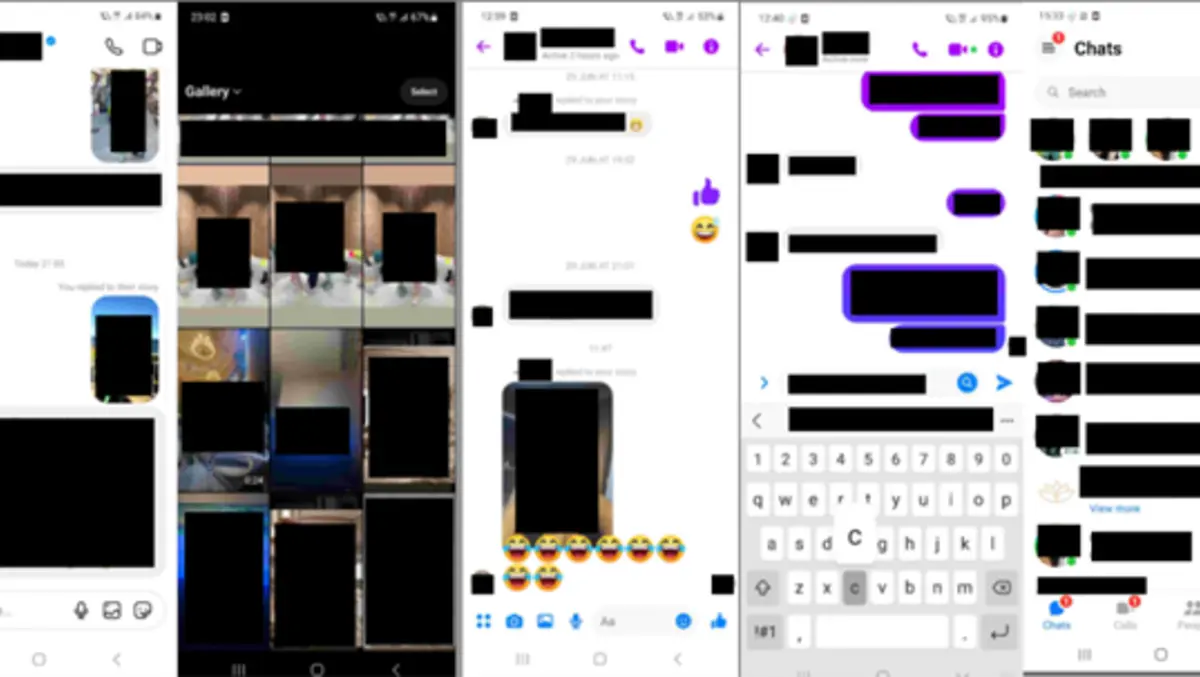
Cybersecurity researcher Jeremiah Fowler and ExpressVPN have disclosed a data leak linked to suspected stalkerware that exposed private communications and images from a prominent European celebrity's device. The database contained 86,859 images that appeared to capture activity across messaging and social media apps.
The publicly accessible database had no password protection and included screenshots that appeared to show conversations on Facebook, WhatsApp, Instagram and TikTok. It also contained what appeared to be intimate exchanges, contact details, emails and images of documents such as invoices, receipts and identification records.
According to the findings, the exposed storage system was named after a known spyware service marketed as monitoring software. The researchers said the database did not appear to belong to that provider, but instead seemed to have been created by an individual using malicious software to monitor a single victim.
The victim was described as a prominent European celebrity, entrepreneur and media personality. The records also included exchanges with models, influencers, celebrities, friends, family members and business associates, though no names were disclosed.
The case highlights the role of stalkerware, a category of spyware installed on phones, tablets or computers to monitor a user without their knowledge or consent. Such software can capture messages, call logs, locations, app activity, photos and social media use. In some cases, it can also activate microphones or cameras.
In this case, Fowler said the person managing the malicious software appeared to have misconfigured the database's access controls, leaving the images and conversations open to anyone with an internet connection. Because installing stalkerware without permission may constitute a criminal offence, he said he contacted law enforcement and notified the victim using phone numbers visible in the captured material.
How it worked
Stalkerware usually runs in the background and tries to avoid detection by disguising itself as a system process or hiding its icon. Once installed, it can request broad device permissions, allowing it to collect data continuously. That data is typically transmitted to a remote server or online dashboard for review by the person who installed it.
The report said some forms of the software can intercept notifications, record audio, capture keystrokes and take periodic screenshots. Encryption in messaging apps does not prevent this kind of surveillance once content is displayed on a device, because the software can record what appears on the screen.
Several jurisdictions treat the unauthorised use of such software as a criminal matter under laws covering computer misuse, unauthorised access, wiretapping and data protection. Australia is among the countries that classify installing stalkerware on another person's device without permission as a criminal offence, with penalties that can include prison terms of up to 10 years.
Warning signs
Researchers said victims may not realise monitoring software has been installed, but some signs can point to compromise. These include unusual battery drain, overheating, increased data use, unfamiliar apps, unexpected pop-ups, slower performance, device restarts and unusual permission requests.
Behavioural clues can also matter. If another person appears to know details about locations, conversations or activities that they should not know, it may be a sign a device is being monitored.
Recommended steps include keeping physical control of devices, using strong passwords, biometric authentication and multi-factor authentication, and making sure operating systems and apps stay updated. Users who suspect spyware are advised to review installed apps, scan devices with security software, and check device administrator and accessibility settings for unusual permissions.
A factory reset can remove hidden spyware, although restoring from a compromised cloud backup may reintroduce the problem. In cases involving harassment or safety concerns, researchers said users may need to report the issue to authorities before removing the software so evidence can be preserved.
Fowler said the case should not be viewed as a problem limited to public figures. "This case highlights how easily personal communications and online interactions can be monitored when malicious software is present. My intention is to highlight these cybersecurity threats and provide guidance on how to identify and mitigate similar forms of digital surveillance," he said.