
ReliaQuest warns of BaoLoader surge & trust attacks
ReliaQuest has reported a rise in malware campaigns that rely on manufactured trust and user interaction, alongside a continued decline in ransomware victim counts posted to data-leak sites.
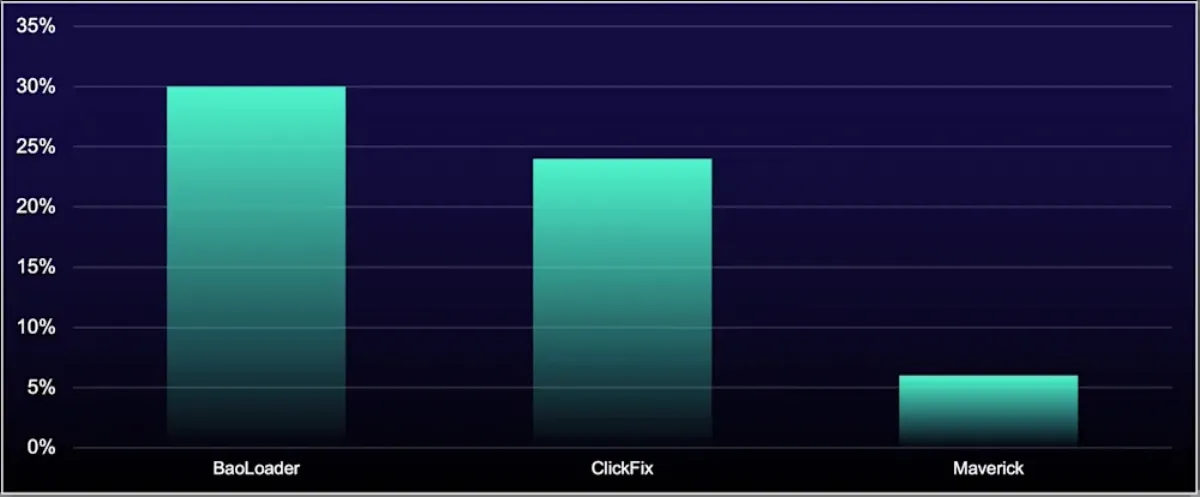
The company said "BaoLoader" dominated incident volumes during its latest quarterly review period and drove the three most common initial access techniques it tracked: spearphishing links, spearphishing attachments, and drive-by compromise. It said other prominent threats, including "ClickFix" and "Maverick", followed similar patterns that focused on social engineering and credential theft.
ReliaQuest said attackers leaned on "trust exploitation" rather than zero-day vulnerabilities during the period. It said this trend increased the importance of monitoring for anomalous behaviour rather than relying on indicators that label files or certificates as suspicious.
BaoLoader surge
ReliaQuest described BaoLoader as a modular loader that blended into normal enterprise activity. It said campaigns used code-signing, malvertising and abuse of legitimate tools.
The report said BaoLoader operators did not focus on stealing or forging code-signing certificates. Instead, it said they registered legitimate businesses in Panama and Malaysia and used them to buy valid code-signing certificates from major certificate authorities. ReliaQuest said the operators obtained at least 26 certificates over seven years and rebranded malware under names such as "AppSuite-PDF," "PDF Editor," "ManualFinder," and "OneStart."
ReliaQuest said public disclosure and certificate revocations did not stop activity. It said the operators adapted and obtained fresh certificates from multiple issuers.
ClickFix and Maverick
ReliaQuest said ClickFix moved from third to second place in prevalence. It characterised ClickFix as a technique that instructs a user to run malicious code directly. It said lures prompted targets to paste obfuscated commands into Windows tools such as Run or File Explorer dialogs.
ReliaQuest said "More convincing lures, bolstered by AI-assisted content and embedded videos, likely contributed to its continued rise."
The report also flagged Maverick as a banking trojan that targets credential theft. It said campaigns delivered Maverick through social engineering. It said the malware used browser monitoring, overlay phishing, keylogging and screenshots. ReliaQuest said Maverick primarily targeted Brazil and raised concerns for financial institutions.
Infostealers shift
ReliaQuest said overall infostealer activity continued to fall sharply. It cited a 67% decline in the previous reporting period and a further 69% decline in the latest period. It linked that change to Lumma infrastructure takedowns.
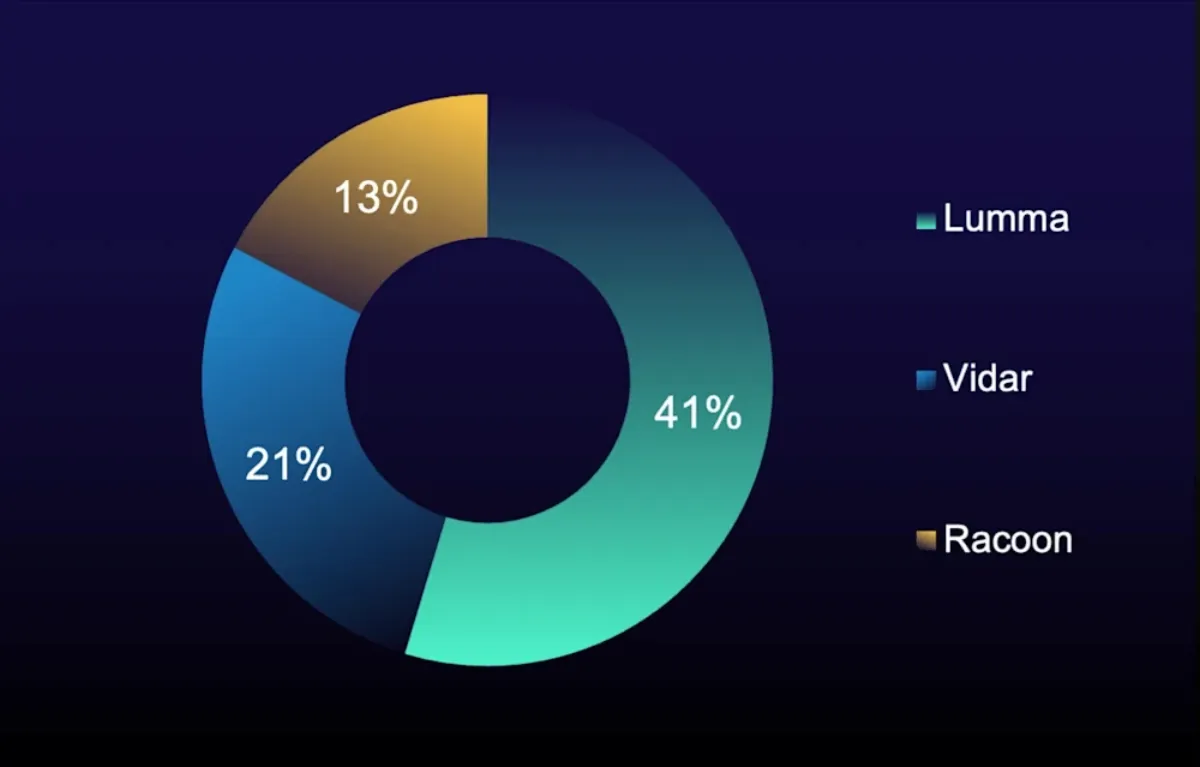
ReliaQuest said lower volumes did not reduce organisational risk. It said "Vidar 2.0" shifted focus from consumer browser credentials to enterprise cloud credentials and authentication keys. It said these credentials often sat on unmanaged or personal devices.
The report said this shift changed the route attackers used to enter corporate environments. It said compromised credentials sourced from home systems and BYOD devices could provide access to production cloud infrastructure.
Ransomware trends
ReliaQuest said ransomware victim counts on data-leak sites fell for a second consecutive period. It said established ransomware groups still succeeded through exploitation of known vulnerabilities in internet-facing devices.
ReliaQuest said "Qilin exploited firewall vulnerabilities CVE-2024-21762 and CVE-2024-55591 throughout the reporting period." It said activity surged to 188 victims in October alone. It also said Akira exploited CVE-2024-40766, which it described as a VPN and firewall vulnerability, and combined it with credential abuse.
The report said the pattern remained consistent across multiple campaigns. It said patches became available, then mass exploitation followed months later.
Sector exposure
ReliaQuest said the professional, scientific, and technical services sector bucked the broader decline in ransomware victim counts. It said victim counts in that segment rose 57% during the period. It said attackers treated trusted partners as attractive entry points.
It also said the top five targeted sectors remained unchanged: professional, scientific, and technical services, manufacturing, health care, technology, and construction.
Evasion and movement
ReliaQuest said defence evasion techniques remained fragmented. It said command obfuscation emerged as the top sub-technique during the period and linked that result to activity from BaoLoader and ClickFix.
It also reported a reduction in the prevalence of Remote Desktop Protocol as a lateral movement technique. It said RDP still ranked first, but its prevalence fell from 54% to 25%. It said SMB and Windows Admin Shares also declined.
"Attackers don't need zero-days when they can manufacture trust itself," said ReliaQuest.
ReliaQuest said it expected volatility in the top malware families to persist into 2026, with core attacker techniques remaining stable while specific tooling changed between reporting periods.
